A recent story has been making the rounds: "Hundreds of Nuclear Radiation Monitors Were Allegedly Hacked by Former Repairmen". Basically, it seems that more than a year ago two disgruntled employees sabotaged +300 radiation monitoring devices, which were part of a nation-wide civil radiation monitoring network (RAR) in Spain. On top of that, they were apparently using the free WiFi of a Starbucks to carry out their activities. Obviously not being the sharpest tool in the box they were eventually caught.
In this story there is a boring part, which is everything related to these guys and their motivations, and a slightly more interesting part which is the underlying technology behind Radiation Monitoring Networks (RMN).
In 2017 I presented at BlackHat USA 'Go Nuclear: Breaking Radiation Monitoring Devices", so I thought it could be interesting to write a brief post to provide some context.
The NeverEnding story
As in most 'disgruntled employee' attacks, the initial motivation behind the sabotage seems to be a 'poorly assessed' reaction to a troubled employment relationship.
According to the information publicly released by the police the attacks started on March 2021. Coincidentally, by using the public procurement portal of the Spanish State, we can find that, in 2020, a public contract to support and maintain the RAR network was announced, as the valid one at that time was about to expire in Feb 2021.
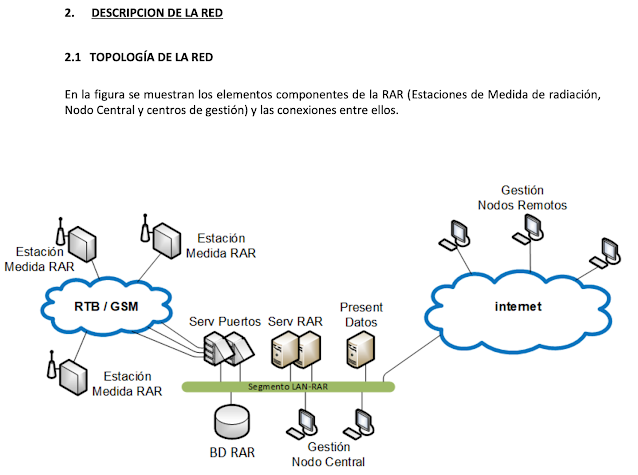
Anyway, if you're interested in the technology, public procurement documents always provide a lot of information when you are researching into nation-wide systems. As expected, it is possible to find some interesting bits of information about the RAR network, including its topology, devices, deployments...
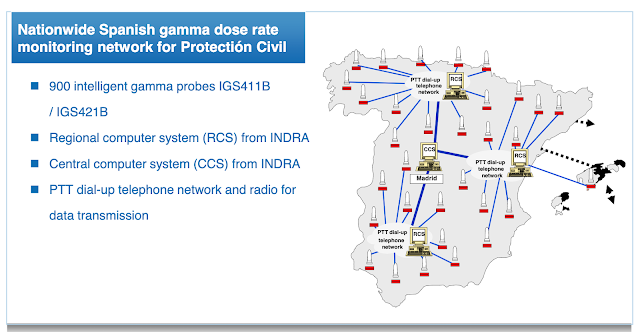
The radiation monitoring devices are provided by Envinet. Indra seems to have developed some Data Acquisition Units as well as the Control System.
 |
| Sensor Units - Envinet |
 |
| Data Acquisition Units - Indra |
 |
| https://www.indracompany.com/sites/default/files/dtu_0.pdf |
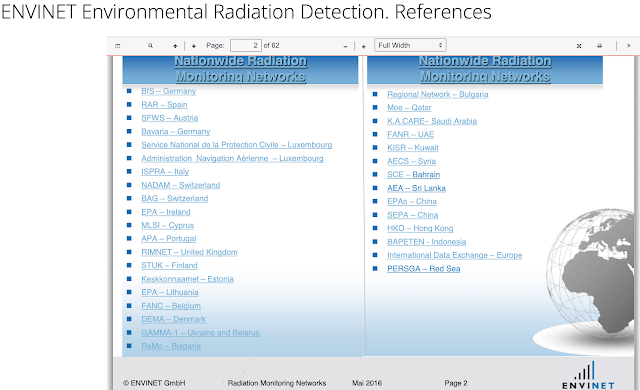
This also seems to match with some documents from Envinet
Attacking Radiation Monitoring Devices
Radioactivity is invisible for the human eye so, as in many other industrial processes, we're essentially relying on the output from a system able to analyze, on our behalf, what is going on in our environment.
Thus, in the context of Radiation Monitoring Instruments, their 'output' will have two main purposes:
1.- Provide data to be consumed by operators
2.- Provide inputs to safety systems
As a result, when I was researching into RMN five years ago, I mainly focused on just two kinds of attacks, which are outlined below. It is important to note that in both cases, the motivation for performing the attack is pretty extreme, so we would be essentially talking about scenarios derived from 'profound conflicts' between nation-states or sophisticated terrorist attacks.
1. - Hide what is happening
By far, this first scenario is usually the worst, as we have to assume the attackers are trying to hide abnormal radiation levels, so we would be already facing a pretty bad ongoing situation. This secondary attack against the RMN would be only aimed to increase the impact of the primary attack.
However, there are some other scenarios, where someone would want to hide abnormal radiation levels just transiently, for instance in radioactive material smuggling scenarios.
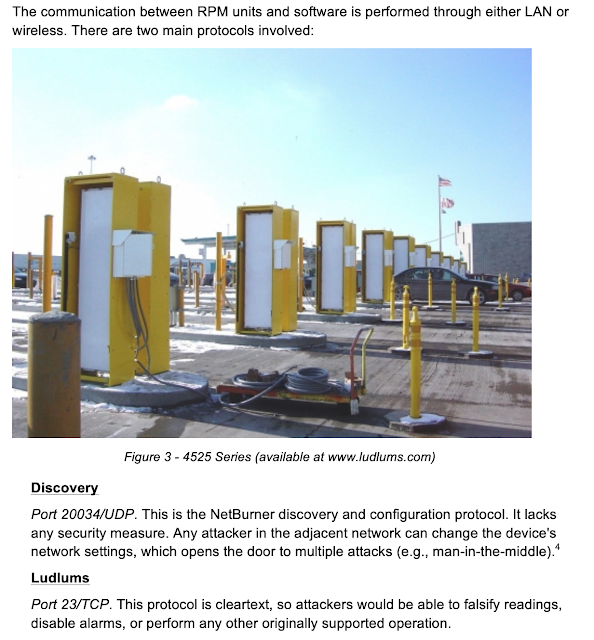
Back in 2017, I looked into some of the Radiation Portal Monitors deployed at US borders, checkpoints or secure facilities, finding backdoors, insecure protocols and the usual stuff.
In addition to borders and ports, Nuclear Power Plants (NPP) are the most common facilities where RMDs are found. However, if a malicious actor is trying to hide abnormal radiation levels in a NPP, quite a few systems need to be compromised.
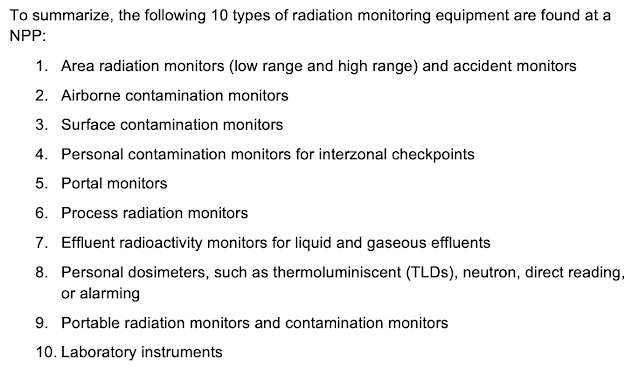 |
| https://www.blackhat.com/docs/us-17/wednesday/us-17-Santamarta-Go-Nuclear-Breaking%20Radition-Monitoring-Devices-wp.pdf (Page 13) |
Therefore, a real-world attack against RMDs in a NPP would likely lie in the next scenario instead.
2. - Show what is not happening
This scenario covers those attacks whose nature is primarily 'cyber'. As I mentioned before, when talking about radiation, our assessment of the situation highly depends on a Radiation Monitoring Instrument's output.
If you can control that output, you could potentially trigger a response that does not correspond to the actual conditions the system is operating at. For instance, in the context of a NPP, the implications of this scenario can be divided in:
- How humans will behave according to the information they are getting
When the operators are reacting to falsified radioactive leakage alarms according to the defined Emergency Action Levels. (i.e Three Mile island incident)
- How safety systems (Class 1E) will react
These systems are provided to ensure the safe shutdown of the reactor or residual heat removal, or to limit the consequences of anticipated operational occurrences.
Final thoughts
In 2017, I managed to compromise the RF security scheme used in RMDs from Mirion, based on Digi's XBEE. This attack allowed to forge arbitrary radiation readings, thus enabling the attackers with the ability to implement some of attacks covered in the scenarios we have been discussing.
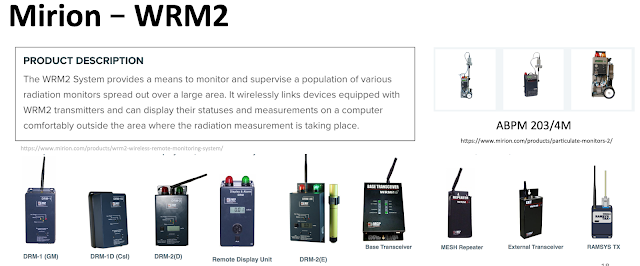 |
| https://www.blackhat.com/docs/us-17/wednesday/us-17-Santamarta-Go-Nuclear-Breaking%20Radition-Monitoring-Devices.pdf (Slide 18) |
In general terms, we should also assume that most of the commercial RMDs out there, and their corresponding networks, are probably an easy target for malicious actors with a strong motivation and plenty of resources.
Although, technically, two guys at a Starbucks disabling the communication of a civil Radiation Monitoring Network endangers the ability to detect if something bad is going on, it may seem worse than it actually is.
On the other hand, I think that the worst-case attack scenarios against this kind of networks are those intended to falsify the 'reality', thus tricking the victim (either operators or safety systems) into triggering a predefined procedure (i.e shutting down a reactor) which has been designed for different conditions.